![[JoGu]](../../JGU.gif) |
CryptologyCryptanalysis of Random Generators: Summary |
|
![[JoGu]](../../JGU.gif) |
CryptologyCryptanalysis of Random Generators: Summary |
|
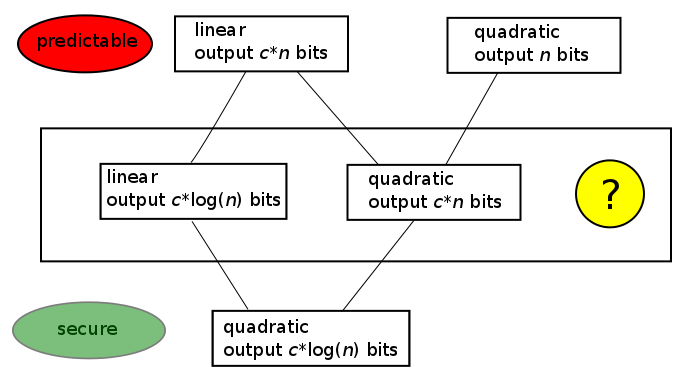
In Sections 1 to 9 we developed a prediction method whose overall workflow is depicted in the following figure:
![[Algorithm for prediction]](PredAlg.png)
One lesson learnt from these results is that for cryptographically secure pseudorandom generation we never should directly use the state of the generator as output. Rather we should insert a transformation between state and output that conceals the state. Section 9 illustrates that simply suppressing some bits—»truncating« or »decimating« the output—might be to weak as an output transformation. In the following section we'll learn about better output transformations.
There is a large twilight zone between pseudorandom generators that promise advantage to the cryptanalyst, and pseudorandom generators that put the cipher designer's mind at ease. In any case we should prefer pseudorandom generators for which both of the procedures
The following chapters present two approaches that are believed to lead to secure random generators: